In this article, we will discuss the different types of risks associated with cloud computing and the strategies businesses can use to protect their data and resources.
Cloud computing is a cornerstone of digital transformation and can deliver fundamental changes to how businesses operate. However, managing risk and achieving good governance in a cloud-enabled world requires a different mindset.
Cloud security is critical since most organizations are already using cloud computing in one form or another. It is a responsibility that is shared between the cloud provider and the customer. Therefore, businesses need to develop a solid cloud cybersecurity strategy to reduce the risk of cloud computing as much as possible and ensure data and systems are protected at rest, in use, and in transit.
We will also explain why risk reduction is the cornerstone of online safety for businesses that want to protect their data and resources.
Table of Contents
What are the different types of risks associated with cloud computing?
When it comes to cloud computing, there are several risks that you should be aware of. Let’s go through each one of them.
1. Unmanaged Attack Surface
An attack surface refers to the exposure of your environment, and when you adopt microservices, it can significantly increase this exposure.
Each workload you add to your cloud infrastructure contributes to the attack surface, potentially leaving it vulnerable to attacks.
Without proper management, your infrastructure may unknowingly be exposed until an attack occurs. This unmanaged attack surface poses several risks, such as unauthorized access to sensitive data, exploitation of software vulnerabilities, and disruption of services.
2. Human Error
According to Gartner, a leading research and advisory company, a staggering 99% of all cloud security failures through 2025 will be due to some form of human error. Human errors can happen at various stages of cloud computing, including configuration, deployment, and management.
One common human error is misconfiguration, where settings and permissions are improperly set. This can lead to data breaches and unauthorized access, posing a significant threat to the security of cloud systems.
Imagine a scenario where a misconfigured firewall allows hackers to gain access to sensitive information, compromising the integrity of an organization’s data.
Another risk is the accidental deletion of critical data or resources. This can have severe consequences, causing significant disruptions to business operations.
For instance, imagine a situation where an employee unintentionally deletes important files or resources, resulting in a loss of valuable data and hindering the organization’s ability to function smoothly.
Moreover, employees may inadvertently fall victim to social engineering attacks, like phishing scams. These attacks trick individuals into disclosing sensitive information or granting unauthorized access.
For example, an employee may unknowingly click on a malicious link in an email, leading to a breach of confidential data.
3. Misconfiguration
Misconfiguration of cloud resources can lead to serious consequences, such as data breaches, service disruptions, and compliance violations.
One common risk is improper access controls, where users are granted excessive permissions or credentials aren’t managed correctly. This can result in unauthorized access to sensitive data or resources.
Another risk is the misalignment of security controls with organizational policies and industry standards. Insufficient encryption settings or the failure to implement multi-factor authentication can make data vulnerable to attacks.
Additionally, misconfigurations in network security settings, like firewall rules or virtual private network (VPN) configurations, can result in unauthorized access or data leakage.
4. Data Breach
Data breaches in cloud computing pose significant risks to the security of your sensitive information.
One type of breach is unauthorized access, where someone gains entry to your data without permission. Weak passwords, stolen credentials, or vulnerabilities in the cloud system can all contribute to this type of breach.
Another risk is data leakage, which occurs when your data is unintentionally exposed to unauthorized parties. This can happen if access controls are misconfigured or if insecure data transfer protocols are used.
Finally, there’s the danger of data loss, where your data becomes permanently inaccessible or corrupted. System failures, natural disasters, or malicious attacks can all lead to this type of loss.
5. Insider Threats
Insider threats can arise from employees, contractors, or business partners who’ve privileged access to sensitive data and systems.
These threats can be deliberate, such as when an employee steals or leaks confidential information, or unintentional, such as when an employee unknowingly exposes sensitive data due to negligence or a lack of awareness.
The risks associated with insider threats encompass unauthorized data and system access, data breaches, intellectual property theft, and harm to the organization’s reputation.
To mitigate these risks, organizations should implement stringent access controls, closely monitor user activity, conduct thorough background checks on employees, and regularly provide security training and awareness programs.
6. Zero-day exploits
A zero-day exploit refers to a security vulnerability in software that’s unknown to the software vendor. This means that attackers can exploit this vulnerability to gain unauthorized access to systems before the vendor has a chance to fix it.
Zero-day exploits can have severe consequences for cloud computing environments, such as compromising sensitive data, disrupting services, or launching additional attacks within the cloud infrastructure.
These risks include the potential for data breaches, loss of customer trust, financial losses, and reputational damage.
To mitigate these risks, organizations should implement robust security measures, such as continuous monitoring, threat intelligence, and timely patching.
7. Advanced Persistent Threats
Cloud computing poses significant risks when it comes to Advanced Persistent Threats (APTs), which are highly skilled attackers that can gain unauthorized access and remain undetected for long periods of time.
- One major risk is data breaches, where APTs can infiltrate cloud systems and steal sensitive information like customer data or intellectual property.
- Another risk is the compromise of cloud infrastructure, where APTs exploit vulnerabilities and gain control over cloud resources, potentially disrupting services or using them for malicious activities.
- Additionally, APTs can severely damage the reputation and credibility of cloud service providers if they’re unable to detect or mitigate these attacks.
To address these risks, organizations must implement robust security measures such as encryption, access controls, and intrusion detection systems to detect and prevent APTs from compromising cloud environments.
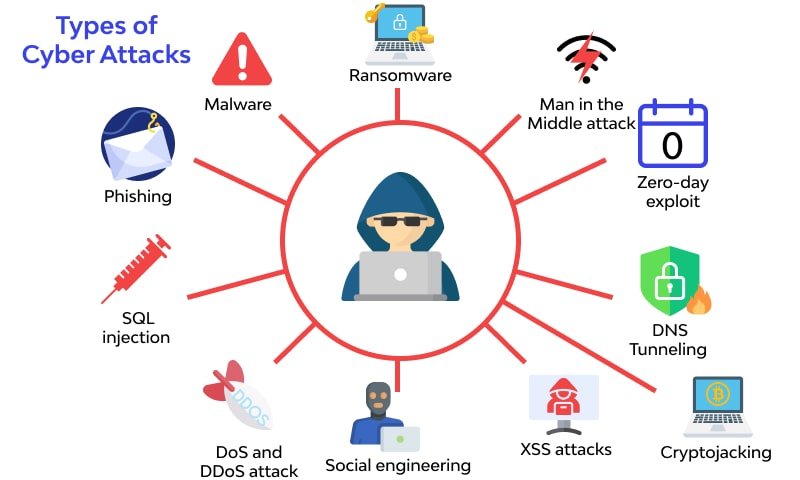
8. Cyberattacks
In the world of cloud computing, cyberattacks pose a significant threat to the security and integrity of your data. One common type of cyberattack is a Distributed Denial of Service (DDoS) attack.
In a DDoS attack, a network gets overwhelmed with traffic, making it inaccessible to genuine users.
Another type is a malware attack, where malicious software infiltrates your cloud system, compromising the confidentiality, integrity, and availability of your data.
Phishing attacks, on the other hand, involve tricking users into divulging sensitive information through deceptive emails or websites.
Data breaches, unauthorized access, and insider threats are also prevalent risks to consider.
What are the strategies businesses can use to protect their data and resources?
To protect your data and resources in the cloud, there are several strategies you can use.
1. Back up regularly
It is important to regularly back up your data and resources to ensure their security. By doing so, you can protect your business from potential data loss caused by cyberattacks, hardware failures, or unexpected disasters.
To select a reliable and secure backup method, consider using cloud storage. Cloud backup services offer automated backups, which means your data will be backed up regularly without the need for manual intervention.
This not only saves time but also reduces the risk of forgetting to back up your data. Plus, cloud storage provides redundancy by storing your data in multiple locations, minimizing the chances of permanent loss.
To further enhance the security of your backups, make sure to encrypt them to prevent unauthorized access. It’s also crucial to regularly test your backups to ensure their integrity and to be prepared for any potential restore needs.
2. Keep software up-to-date
To protect your data and resources, it’s important to keep your software up-to-date. Regularly updating your operating systems, applications, and firmware helps to mitigate the risk of vulnerabilities that attackers can exploit.
When software vendors release updates, they include security patches and bug fixes that address known vulnerabilities.
By promptly installing these updates, you ensure that your software has the latest security measures, reducing the chances of successful attacks.
Updating your software also enhances compatibility with other applications and devices, improving system performance and reliability. To make the update process easier, consider using automated tools that can schedule and install updates for you.
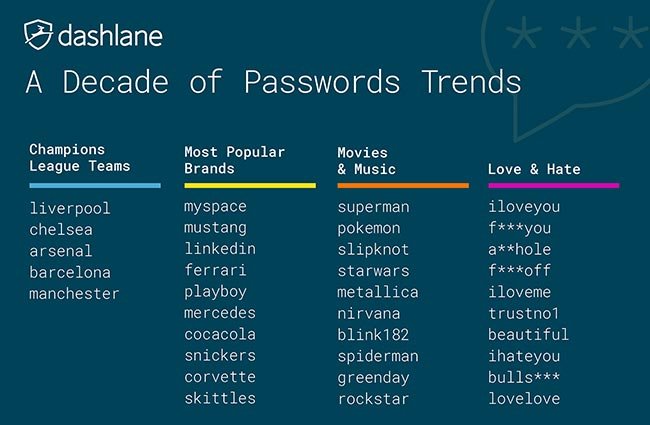
3. Use strong passwords
To protect your data and resources, it’s super important for businesses to update their software regularly and use strong passwords (not your spouce’s name).
When it comes to passwords, it’s important to choose combinations that are unique and difficult for hackers to guess. Avoid using common words or personal information that can be easily deduced. Instead, go for a mix of uppercase and lowercase letters, numbers, and special characters.
Using a password manager is highly recommended as it can securely store and generate strong passwords for all your accounts.
It’s also important to change your passwords on a regular basis to prevent unauthorized access. For added security, consider implementing two-factor authentication, which requires additional verification such as a fingerprint or a one-time passcode.
4. Control access
One strategy that businesses can use is multi-factor authentication (MFA). MFA adds an extra layer of security by requiring users to provide multiple forms of identification, such as a password, fingerprint scan, or a one-time code sent to their mobile device.
This helps to prevent unauthorized access and protect sensitive information.
Another effective strategy is role-based access control (RBAC), which assigns specific permissions and privileges based on an individual’s role within the organization.
By doing so, businesses can ensure that users only have access to the data and resources necessary for their job responsibilities. This helps to minimize the risk of accidental or intentional data breaches.
Additionally, network segmentation can be used to isolate sensitive data and resources from the rest of the network. This prevents unauthorized access and limits the potential damage in case of a security breach.
5. Encrypt data
To ensure the security of your data and resources, it’s essential to implement encryption as a key strategy.
Encryption involves encoding data using complex algorithms, which makes it unreadable without the decryption key.
This helps protect sensitive information from unauthorized access, both when it’s stored (at rest) and when it’s being transmitted (in transit).
There are various effective strategies that businesses can use to implement encryption.
- For example, you can encrypt data at rest by applying encryption algorithms to files stored on local devices or in cloud storage. This ensures that even if someone gains access to the storage, they won’t be able to decipher the encrypted data.
- Also, it’s crucial to encrypt data in transit, especially when transmitting data over the internet. This can be achieved by using secure protocols such as Transport Layer Security (TLS) or Secure Sockets Layer (SSL). These protocols establish a secure connection between the sender and the recipient, ensuring that the data is protected from interception and tampering.
- Managing encryption keys securely is also of utmost importance. It’s recommended to use strong passwords or multifactor authentication to prevent unauthorized access to the decryption keys. This adds an extra layer of security to the encryption process.
- Finally, it’s essential to regularly review and update encryption algorithms and protocols to address any emerging vulnerabilities. This ensures that your data remains protected against evolving threats and ensures the continued effectiveness of your encryption strategy.
6. Train employees
To protect your data and resources, it’s crucial to implement security training for your employees. By providing comprehensive training, you ensure they have the knowledge and skills to effectively identify and respond to security incidents.
Start by educating them on security best practices, such as using strong passwords, being cautious of phishing attempts, and regularly updating software.
Next, teach them how to promptly recognize and report security incidents, as early detection can minimize potential threats.
To reinforce their training, conduct regular security awareness workshops and simulate phishing attacks to test their response.
By investing in employee training, you create a security-conscious culture, significantly reducing the risk of data breaches and other security incidents.
7. Seek professional guidance
If you want to protect your data and resources effectively, it’s important to seek guidance from security experts. These professionals have the expertise to identify potential risks and vulnerabilities in your cloud computing infrastructure.
By working with them, you can develop a comprehensive risk management plan that aligns with your business goals and regulatory requirements. They’ll ensure that your data is properly encrypted and protected, and that your cloud service provider has strong security measures in place.
They can also help you with incident response planning and provide guidance on implementing effective security controls and monitoring tools.
Seeking professional guidance not only ensures the safety of your data and resources but also gives you peace of mind, knowing that you have taken necessary steps to mitigate risks in your cloud environment.
How CyberCX’s risk reduction solutions can help businesses protect their data and resources?
CyberCX offers a range of risk reduction solutions that are designed to safeguard your valuable information from potential threats.
For example, with their advanced cybersecurity measures, you can rest assured that your data will remain confidential and secure.
CyberCX’s expertise in governance, risk, and compliance services allows them to assess and identify any potential risks to your organization, enabling you to take proactive steps to mitigate these threats.
They also provide business continuity planning services to ensure that your operations can continue smoothly, even in the face of disruptions.
What are the benefits of CyberCX’s risk reduction solutions and how they can help businesses reduce their risk?
CyberCX’s risk reduction solutions offer several benefits that can help businesses lower their risk. For example:
1. Preparedness
CyberCX offers a range of solutions that are designed to enhance your organization’s readiness to tackle unexpected challenges.
By utilizing their comprehensive plans, you can ensure that your organization is well-prepared to navigate through complex scenarios.
These solutions enable you to identify potential risks, develop effective response strategies, and establish robust contingency plans.
2. Risk mitigation
CyberCX’s risk reduction solutions offer a comprehensive and proactive approach to risk management.
With their range of solutions, including cyber threat protection, data breach prevention, and regulatory compliance, CyberCX provides robust protection against potential risks.
One of the key benefits of CyberCX’s risk reduction solutions is their ability to identify and assess vulnerabilities in your organization’s infrastructure and systems.
Through advanced threat intelligence and continuous monitoring, CyberCX can proactively detect and respond to potential risks, reducing the likelihood of a security incident.
This proactive approach keeps businesses ahead of cyber threats and safeguards their operations and reputation.
Moreover, CyberCX’s risk reduction solutions provide actionable insights and recommendations to enhance security.
By analyzing data and identifying patterns, CyberCX helps organizations strengthen their defenses and implement effective risk mitigation strategies.
This proactive and data-driven approach reduces overall risk exposure and ensures business continuity.
Finally, CyberCX offers incident response services to help organizations effectively manage and recover from security incidents.
Their experienced team of professionals swiftly responds to incidents, minimizing the impact and aiding in the recovery process. This ensures businesses can quickly resume operations and minimize financial or reputational damage.
3. Cost effectiveness
Taking a proactive approach to risk management helps you avoid the significant expenses associated with incident response, remediation, and recovery efforts.
With CyberCX’s comprehensive and integrated approach, you can optimize your cybersecurity investments, ensuring efficient allocation of resources for maximum protection.
4. Achieve long-term resilience
CyberCX’s risk reduction solutions, effectively minimize the financial impact of cyber threats and help prevent costly data breaches, system disruptions, and reputational damage.
By leveraging advanced technologies and industry best practices, CyberCX helps businesses identify potential vulnerabilities in their IT systems and develop tailored strategies to address them.
This includes implementing robust security measures like firewalls, intrusion detection systems, and encryption protocols to protect sensitive data and prevent unauthorized access.
Additionally, CyberCX offers continuous monitoring and threat intelligence services, keeping businesses informed about emerging threats and enabling them to take proactive measures.
Frequently Asked Questions
What are the 3 types of Cloud Computing?
The three main types of cloud computing are:
– Infrastructure as a Service (IaaS): With IaaS, companies control their own computing, networking, and storing components without having to manage them on-premises physically.
– Platform as a Service (PaaS): PaaS provides developers with a framework to build custom applications.
– Software as a Service (SaaS): SaaS avails internet-enabled software to organizations via a third party.
How do vendors charge for cloud services?
Cloud service vendors typically charge based on several factors:
– Types and quantity of services and computing resources required: This includes the types of services (IaaS, PaaS, SaaS) and the amount of computing power needed.
– Data transfer rates and storage needs: Costs are based on the amount of data transferred in or out of the cloud infrastructure and the storage used.
– Networking: Cloud computing services require a robust network infrastructure for interconnectivity.
– Hardware and Maintenance: Providers need to invest in hardware (drives, memory, processors, servers, routers, firewalls, etc.), continuous updates, and maintenance.
– Hidden Charges: These can include data overages, exit fees, region and availability zones, and support costs.
– On-Demand: This is a pay-as-you-go plan billed on a per-second or per-hour basis, depending on usage.
What is the difference between reserved and spot instances?
Reserved Instances and Spot Instances are two types of cloud computing services that differ mainly in terms of cost, availability, and usage.
Reserved Instances:
– Reserved Instances are configured almost exactly like On-Demand Instances.
– The only difference is that instead of requesting instances as and when you need them, you “reserve” instances for either one year or three years.
– Reserved Instances offer up to 72% decreased rates and high availability, but with long commitment periods.
Spot Instances:
– Spot Instances involve bidding on excess or unused capacity available with AWS and paying only for the time you use it.
– While spot instance prices fluctuate based on the supply and demand of the current market, the prices are usually lesser than on-demand and reserved instances.
– With spot instances, you can get up to 90% off with no required long-term commitment.
However, there is a catch that you need to be careful about: AWS can terminate spot instances at any time and with a short termination notice. This happens when the capacity demand increases or your bid for the spot instance gets outbid. When AWS wants to reclaim a spot instance, it will send a two-minute warning through CloudWatch Events and instance metadata. You can use these two minutes to save the application state, upload log files, or drain any presently running containers.
– Spot instances are suitable for workloads that are fault-tolerant, non-critical, and flexible since these instances can get interrupted easily without much notice.
– Spot instances are ideal for workloads that are flexible, stateless, fault-tolerant, and non-critical, such as batch processing, testing, or development.
– Overall, it is advisable not to run any kind of business-critical applications on the spot instances.
Final Take
Cloud computing introduces risks that businesses must address to protect their data and resources.
To enhance security measures, businesses can implement effective strategies like CyberCX’s risk reduction solutions. By leveraging these solutions, organizations can minimize their risk exposure and benefit from increased data protection and resource safeguarding.
It’s crucial for businesses to prioritize risk management in their cloud computing strategies to ensure the safety and integrity of their valuable assets. By doing so, they can confidently navigate the complexities of the digital landscape and safeguard their crucial information.
LATEST POSTS
- Zodiac Magic Angel Drop Unveils Exclusive Skins and Esports-Ready Gameplay in Citizen Conflict Alpha 4.0
- Velo Web3+ and Inery Collaborate for Enhanced Web3.0 Data Management
- NVIDIA Inception Welcomes Presearch.com: A Game-Changer in the Crypto Search Space
- Sovereign Wallet’s Innovative “Chained Cash” Technology Redefines Offline CBDC Payments
- SwissGold Crypto AG: Transforming Wealth Preservation with Gold-Backed NFTs
Previous Articles:
- EarnTV: Transforming Video Streaming Through Blockchain Innovation
- LimeVPN Review: Details, Features and Pricing
- Aragon Association Announces Dissolution and Liquidity Provision for ANT Redemption
- Zodiac Magic Angel Drop Unveils Exclusive Skins and Esports-Ready Gameplay in Citizen Conflict Alpha 4.0
- Velo Web3+ and Inery Collaborate for Enhanced Web3.0 Data Management
