This article will describe what is Network Security Using Cryptography and everything you need to know before you start implementing.
The arrival of the e-commerce industry has led to an increase in social networking, e-commerce transactions and online business. Hence a vast amount of data is being transmitted on the wireless network.
Security of this data-in-transit is of utmost importance because if there is a data breach than the damage is bound to be collateral.
Network security protects both hardware and software devices against unauthorised hackers. It protects files, directories and software codes from being compromised by unknown sources.
It secures the network systems and workstations from harmful spyware, malware attacks, and data theft. In short, it takes all preventive measures to protect the network infrastructure and helps create a secure environment for users and computers. One such network security layer is called Cryptography.
About Cryptography
Cryptography is all about encryption, just like SSL security. Various types of SSL certificates secure your website in multiple ways.
Example: Multi-Domain Wildcard SSL certificate secures multiple domains and sub-domains with a single certificate.
Cryptography also uses encryption algorithms to secure sensitive data passing through your network. No one except the intended recipient can decrypt the data and read it. Since we are all moving towards digitalization, there is a phenomenal increase in cyber-crime, and cryptography is one such security decoding tool which is used to decrypt encrypted messages.
It develops protocols that secure your wireless communication in the presence of adversaries. Adversaries are malicious third parties that try to gain unauthorized access to your valuable information, thus causing the breach of security.
Role of Cryptography in Network Securit
The basic principles of cryptography are to ensure data confidentiality; data integrity, authentication and non-repudiation.
Data Confidentiality:
Cryptography protects data by hiding messages from cyber-criminals by using vital cryptographic techniques.
Data Integrity:
Cryptographic tools protect data integrity with hashing technique. It ensures that data is not modified by using cryptographic checksums for verification of data integrity.
Authentication:
Integrity Authentication and Source Authentication are two types of authentication services provided by cryptography. Integrity authentication is used to check data modification whereas; source authentication verifies user identity of the creator of data.
Non-Repudiation
Non-repudiation service, which is used in network security provides evidence of data origin and authenticity of digital signatures. Cryptographic hash functions preserve that integrity by hashing the document and transmitting the same with a shared encryption key. Non-repudiation ensures that the person/party associated with the agreement cannot deny the genuinity of the signature or document.
Components of Cryptographic Systems
The below image shows how the cryptosystems work, how the sender sends a plain text which is encrypted with an encryption algorithm and encryption key, to form a cypher text.
This cypher text is in a non-readable format, and requires decryption of the text, for making it readable. Hence the cypher text is decrypted with the decryption algorithm and decryption key to form plain text for the receiver to read the secret message.
Hence only the sender and the receiver will be able to view the data.
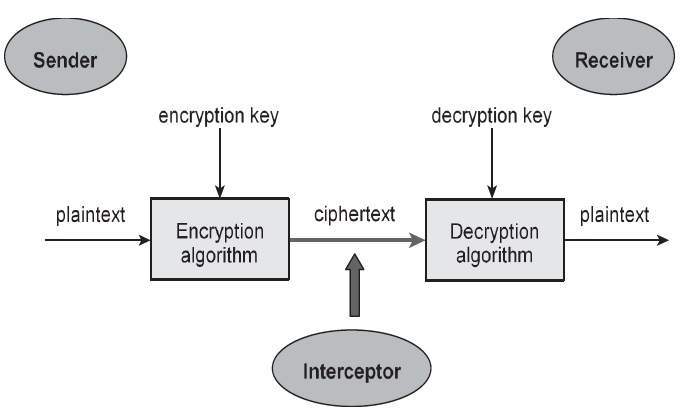
- Plain Text: The data-in-transit which needs to be protected from fraudsters.
- Cypher Text: The encrypted text is also called ciphertext because it is in a non-readable format, and can be read only with proper code, which can decrypt the ciphertext to make it readable.
- Encryption Algorithm: Encryption procedure converts the plain text into ciphertext. This cryptographic algorithm uses the plain text and encryption key (generated during the encryption process) as an input to create ciphertext.
- Decryption Algorithm: This algorithm generates plain text with the help of ciphertext and the decryption key. Without the use of the correct key, it is impossible to decrypt the ciphertext. In short, the decryption algorithm process is a reverse of the encryption algorithm process.
- Encryption Key: This key is used by the sender, to encrypt the plain text along with the encryption algorithm, to generate a ciphertext.
- Decryption Key: This key is used by the receiver, to decrypt the ciphertext along with the decryption algorithm, to generate a plain text.
Who tries to force entry into your network, can view the ciphertext and can use the decryption algorithm, but if they do not have the decryption key, they will never be able to see the cipher data.
Types of Cryptography
There are three types of Cryptography which secure your network. They are Secret Key, Public Key, and Hash Function.
Secret Key (Symmetric Key)
Secret key cryptography is also known as symmetric-key cryptography. Here both the sender and the receiver use only one key to encrypt and decrypt messages.
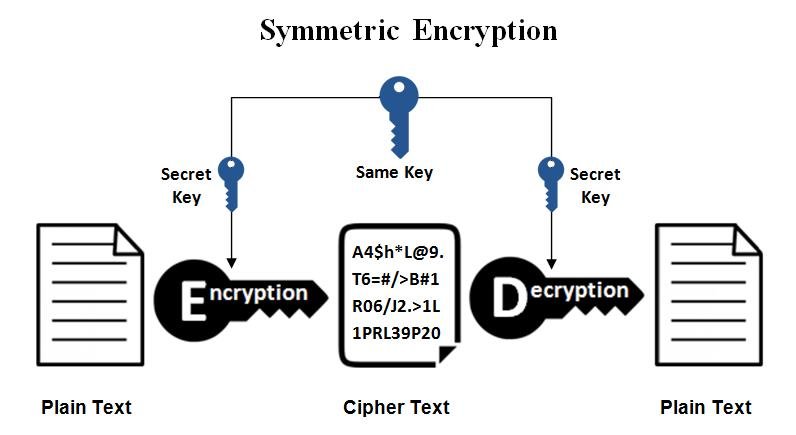
Examples: Triple-DES (3DES), Digital Encryption Standard (DES), AES, RC5, BLOWFISH etc.
Stream Ciphers or Block Ciphers classify this cryptography.
- Stream Ciphers: Stream cyphers work on a single byte (word) at a time. Here the unique key which encrypts and decrypts data is continuously changing. Stream cyphers encrypt random sequences with individual bytes of plain text to create cypher text.
- Block Ciphers: Block Ciphers, on the other hand, encrypts an entire block (64 bits) at one time, just as the name suggests. It uses the same fixed key on each block to create the cypher text.
Features of symmetric key encryption for cryptosystem are
- The common key is shared with the respective persons before the information exchange.
- It’s wise to change keys frequently to prevent network attacks.
- Since a robust mechanism is involved in exchanging keys, it is expensive.
- Since crucial length is shorter in symmetric key encryption, encrypt – decrypt process becomes faster.
- It requires less processing power as compared to asymmetric encryption.
Hazards of Symmetric Key Cryptosystem
Critical Establishment (Key Exchange): Since both the sender and receiver share the same secret key, both the parties must be equipped with a secure mechanism for the same.
Trust: This cryptosystem is based on trust. Trust issues can happen, if the key is lost or stolen by one party and the same is not reported to another party. Sometimes you need to share the key with unknown sources too, which makes asymmetric key encryption a preferred choice.
Pubic Key (Asymmetric Key):
Public key cryptography is also known as asymmetric-key cryptography. Here two different cryptographic keys (public and private key) are used to encrypt and decrypt the data.
The public key is given to all who want to send an encrypted message, whereas the private key for decrypting the message lies with only one person. Public key cryptography is better secured that private key cryptography and hence is more frequently used in daily practices.

Examples: EIGamal, DSA, PKCS, Elliptic curve techniques etc.
Features of asymmetric key encryption for cryptosystem
- The private key must be firmly secured, and the public key must be put in the public repository.
- It authenticates messages and allows non-repudiation to detect compromised signals.
- The main strength lies in these user-related keys, which are not computed to find each other.
- The process of encryption and decryption in asymmetric key encryption is slower than symmetric key encryption because of its sizeable key length (bit length).
- It requires a higher processing power as compared to symmetric key encryption.
Hazards of Asymmetric Key Cryptosystem
The public key allocated to the user for sending messages needs to be trustworthy and not spoofed by a cyber-criminal. PKI (Public Key Infrastructure) helps in authenticating the same.
- If the private key is lost, your message can never be decrypted.
- The process becomes slow in case of decryption of bulk messages.
- A significant security lapse is when your private key is attacked; the unauthorized attacker can view all your messages.
Cryptographic Hashing
Hashing is a network security function which involves a mathematical process to convert data into a string of text. This method of cryptography hashes all sorts and types of data irrespective of its length; and the result is a fixed-size bit string.
Thus hashing protects tampering of data-in-transit, keeping it in a safe zone. Hashing assures the authentication of data.
Secure Hashing Algorithm (SHA-2 and SHA-3), Message Direct Algorithm 5 (MD5), BLAKE2 etc.
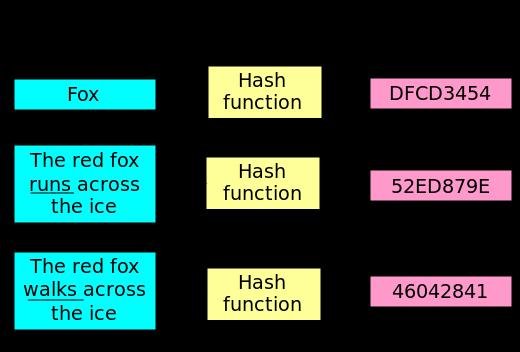
Properties of Cryptographic Hashing
- Input hashes do not collide with output hashes.
- It is tough to guess the input hash value based on the output hash value.
Characteristics of Hash Function
- The hash value depends on the data, which has to be hashed.
- Hashing uses the entire input data.
- This function equally distributes data across all the hash values.
Network Security Using Cryptography
The concept of network security and cryptography is the same. I.e. securing and protecting network and communications, including data transmissions on the internet. Network Security consists of protecting the entire network infrastructure and its resources from intruders by constant monitoring and encryption.
Encryption security used in cryptography to secures all electronic transactions like digital signatures, data-in-transit, bank/credit card account numbers, passwords and all other sensitive information. Still, it also helps create a trustworthy environment by ensuring confidentiality.
The mathematical algorithms used in encrypting and decrypting data keep cyber-criminals away from penetrating your network and misusing your data. Cryptography’s sharp end – to – end encryption security keeps your business and financial deals safe and hence it is a favourite in banking sectors, e-commerce industries, credit card companies, and other businesses having ample electronic transactions.
Its components, crypto, and logos have made cryptography an emerging technology for securing the network. Its security protocols are also used in digital signatures, time stamping, electronic money transfers, and disk encryptions.
Conclusion
In this article, I have elaborated on multiple cryptographic techniques that help in securing your network. Network Security Using Cryptography though the e-commerce industry and e-net are the future of digitalization, cryptography is undoubtedly the future of network security.
Image by Gerd Altmann from Pixabay
Previous Articles:
- Mercuriex Cryptocurrency Exchange Launches New Utility Token, SURF
- Fungibility: Bitcoin Mixers Favorite Term That No One Understands
- Crypto can’t thrive in the real world – but stablecoins can
- Cryptocurrency Top Security Risk Concerns: What You Can Do to Protect Your Crypto
- How has Bitcoin of America Changed the Cryptocurrency Industry?
